软件逆向-驱动挂钩所有内核导出函数来进行驱动逻辑分析
推荐 原创【软件逆向-驱动挂钩所有内核导出函数来进行驱动逻辑分析】此文章归类为:软件逆向。
驱动挂钩所有内核导出函数来进行驱动逻辑分析
太长不看
- 内核hook框架 282K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6Y4K9i4c8Z5N6h3u0Q4x3X3g2U0L8$3#2Q4x3V1k6K6L8h3q4D9L8s2A6Z5L8$3&6Y4i4K6u0r3K9$3g2J5L8X3g2D9K9r3!0G2K9H3`.`.
- 使用上面框架进行对驱动所有导出函数进行挂钩,从而很方便地对驱动进行分析 508K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6Y4K9i4c8Z5N6h3u0Q4x3X3g2U0L8$3#2Q4x3V1k6K6L8h3q4D9L8s2A6Z5L8$3&6Y4i4K6u0r3K9$3g2J5L8X3g2D9i4K6g2X3L8h3!0F1K9i4c8G2M7R3`.`.
- 欢迎大家来star,感恩!您的小星星是对我莫大的鼓励!
引言
三年前我写了一个用来在内核做 inlinehook 的项目 [原创]开源一个自己写的简易的windows内核hook框架 。写这个框架的初衷是我发现并没有一个很好用的在windows内核进行 inlinehook 的框架。米松大佬曾经把 detours 移植到了内核 9abK9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6Y4K9i4c8Z5N6h3u0Q4x3X3g2U0L8$3#2Q4x3V1k6y4K9i4u0G2d9$3q4C8N6g2)9J5c8V1c8W2N6r3!0#2M7Y4y4j5 ,这个框架很好用,但是 detours 本身是为了三环挂钩开发的,其设计之初好像并没有考虑内核挂钩的特殊情况,因此如果出现了4字节相对寻址,其还是会按照三环的逻辑来修复这个4字节寻址。而此时4字节寻址已经无论如何满足不了需求了,因为申请的内存在2GB开外。在该项目的issue区可以看到 2d0K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6Y4K9i4c8Z5N6h3u0Q4x3X3g2U0L8$3#2Q4x3V1k6y4K9i4u0G2d9$3q4C8N6g2)9J5c8V1c8W2N6r3!0#2M7Y4y4j5i4K6u0r3K9i4y4K6N6h3g2K6i4K6u0r3x3R3`.`. 挂钩 MmIsAddressValid 失败的情况。这里就是因为有一个E8 call,detoursX 修复相对地址失败了。如图是hook之前的情况
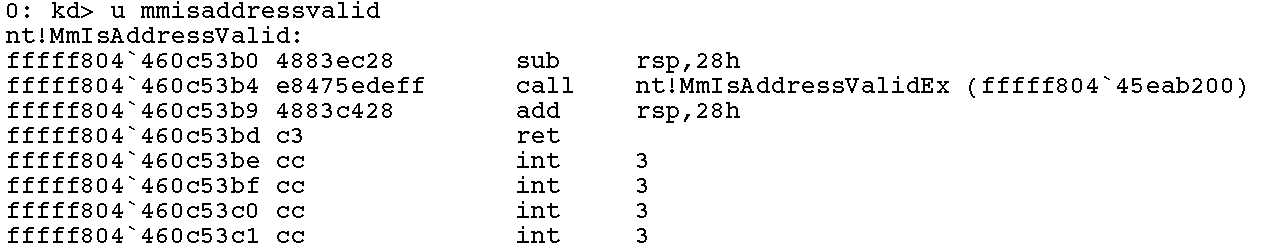
hook之后,这个e8 call并没有被正确修复,导致跳到不存在的地址
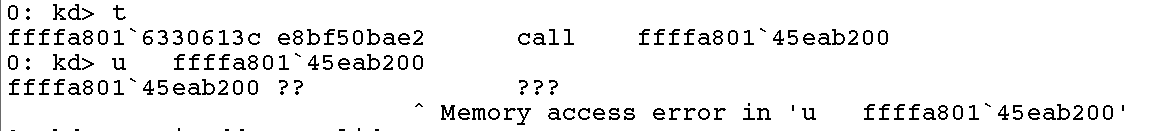
事实上,对于这种有相对寻址的情况,并不能简单修复4字节的相对地址。因为内核是一个很宽广的空间,4字节只能寻址4GB内存,内核是申请不到离得这么近的内存地址用来存放 trampoline 的。为了解决这个问题,我写了一个hook框架,在框架中对相对寻址进行了特判,使得所有相对寻址都能正确找到对应的位置。
三年前写的只是一个简单的框架,后来慢慢适配了很多特殊情况,并修改了一些存在的bug,慢慢提高了整个框架的鲁棒性。
KernelHook
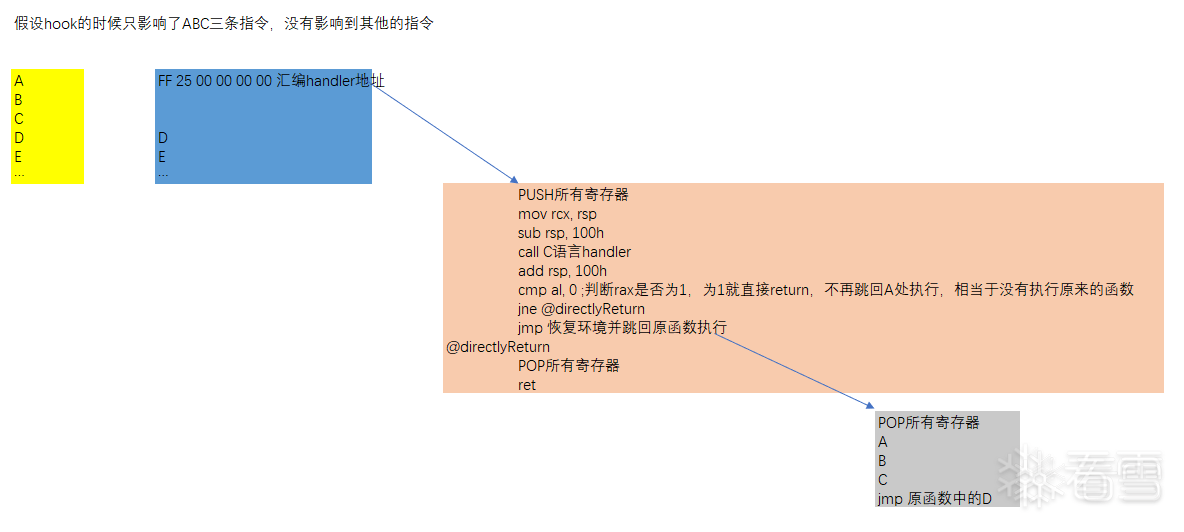
在函数中没有任何相对寻址指令时的 hook 流程
如图,假设未被hook的代码如黄色图块显示。代码顺序为ABCDE,假设ABC三条指令加起来长度大于14字节,可以放下 ff 25 00 00 00 00 00 00 00 00 00 00 00 00 这个跳转。本框架会自动识别这三条代码的长度,然后将其替换为一个 ff25 jmp。其跳到自己申请的一块空间。跳转完成之后首先进行环境的保存,将所有寄存器保存到栈中。然后call一个C语言写的callback函数。可以在这个函数中进行相应的操作。如果这个函数的返回值是 FALSE ,则跳转回原函数处进行执行。如果为 TRUE ,则直接return,不再执行原函数。如果需要执行原函数,则重新POP所有之前保存的寄存器,然后执行 A B C 三条语句,最后通过一个 ff25 jmp跳到原函数中的下一行处执行(在此示例中是D处)。
代码中存在相对寻址跳转的情况
本框架适配了大量相对跳转的模式,如7X XX && E1 xx && E2 xx && E3 xx && EB xx一字节短跳,0F 8X XX XX XX XX四字节相对跳转,E8 E9四字节短跳和call等。这些情况的处理方法都如下图所示
假设 ABC 三条语句中,只有B这一条语句是一个使用了相对跳转的语句。这里用 74 XX 这个JE跳转举例。
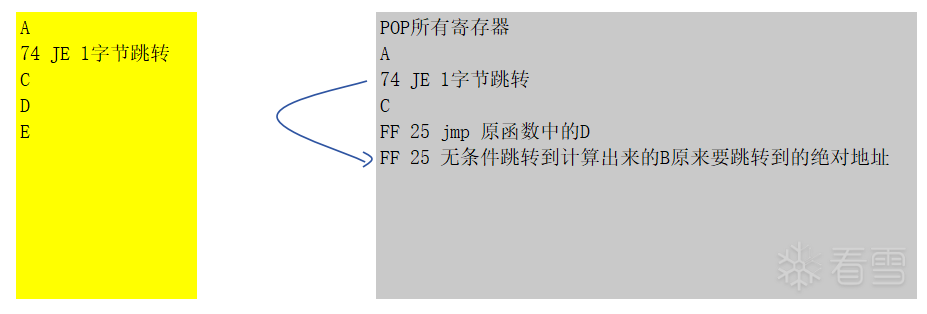
如图,本框架会自动计算出来跳转的目的地的绝对地址,然后生成一条 FF25 无条件跳转语句放在 shellcode 的最末尾。然后把74跳转的目标改为这一条FF25跳转指令的相对地址。这样的话,如果这条JE跳转条件成立,会跳转到FF25指令处,然后FF25跳转到原先的绝对地址处。这样保证了逻辑的正确性。其他1字节、4字节的相对寻址跳转都使用了这样的思想来进行修正。
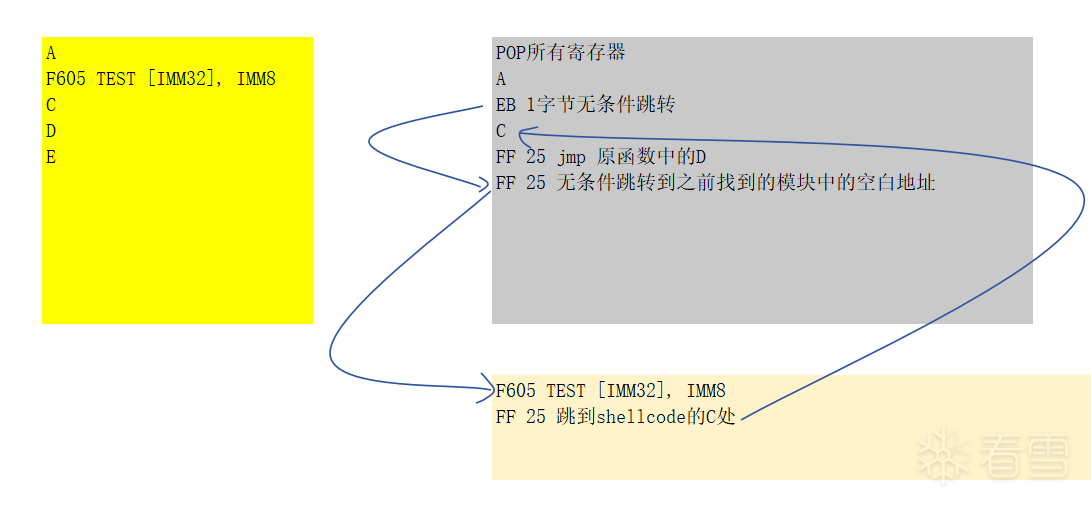
代码中存在使用4字节相对寻址的 test、lea、mov的情况
这种情况比较复杂,因为这些代码并不像跳转指令那样可以简单使用FF25作为trampoline跳回真正的绝对地址。而且这些指令并不存在可以使用绝对地址寻址的指令版本,因此也不能将其特殊改造为绝对寻址版本。在本框架中,处理的方法如下:16字节对齐地查找被hook的模块中全0的地址,然后把相对寻址的代码复制过去,因为这时的地址在对应模块地址内部,因此可以完成相对寻址的执行。逻辑如图
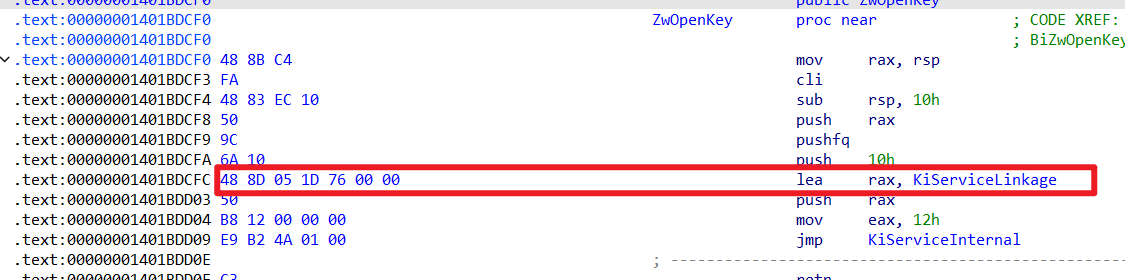
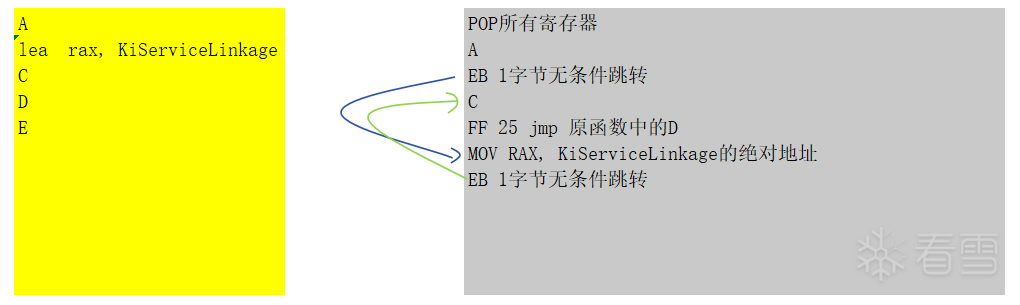
特殊处理 48 8d 05 LEA
内核中大量存在 48 8D 05这种相对寻址代码。主要出现在Zw函数中。如果所有的函数都使用寻找模块内空白地址进行跳转的方法,会出现模块内空白地址耗尽导致无法hook的问题,因此这里对这种情况做了一下特判。把这个LEA改成了一个 48 B8的 MOV RAX, IMM64。
如下图所示
HOOK大部分导出函数,实现内核的详细监控
特殊情况处理
有了上面的hook框架,就可以考虑对内核的一些函数进行hook来进行对特定驱动的系统函数调用流程分析了。首先需要专门处理一种特殊情况,在这种情况下,不能直接hook函数。那就是,如果有其他代码会跳转到开头需要覆盖的指令的中间,就不能直接对函数进行hook。说起来有点拗口,但是举一个例子就明白了,如下
比如这个函数
RtlUnalignedStringCchLengthW,可以看到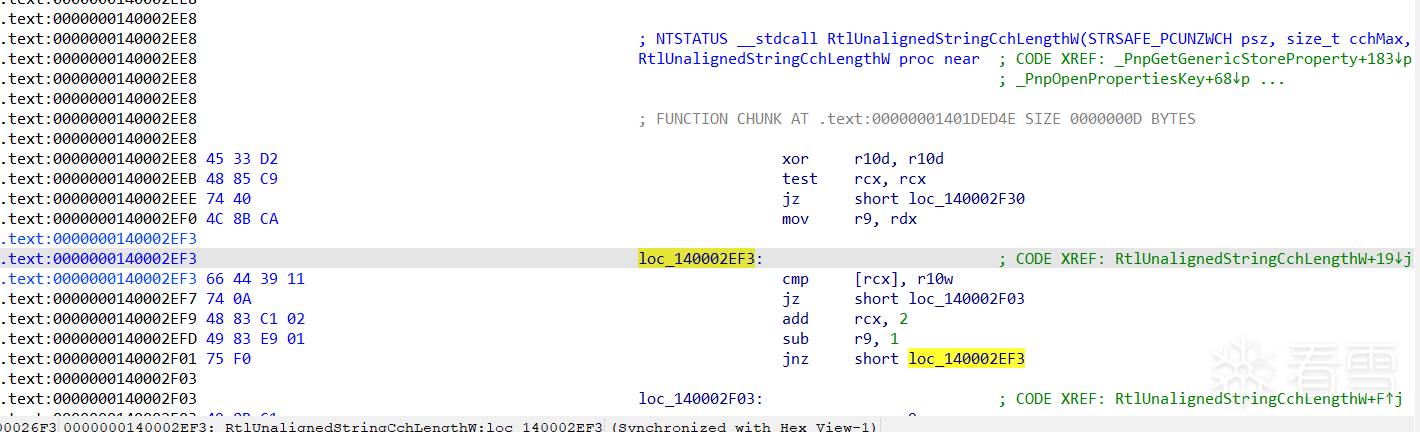
在开头第12个字节有一个基本块,在其他地方有跳转到这个基本块的代码。在这种情况下,如果直接填入 ff25(14个字节),会覆盖这个位置。而后面的jnz还是有可能跳转到这个地址,这就会导致跳转到corrupted memory,而产生不可控的后果。
解决这个问题的办法是写一个IDA脚本对这种情况进行特判,一旦函数开头前14个字节出现了可能被其他基本块跳转到的基本块,就标记为False,不处理这个函数。判断函数如下
12345678910defhas_xrefs_to_middle(start_ea, end_ea):instr_size=idc.get_item_size(start_ea)start_ea+=instr_sizewhilestart_ea < end_ea:t=idautils.CodeRefsTo(start_ea,False)foriint:returnTrueinstr_size=idc.get_item_size(start_ea)start_ea+=instr_sizereturnFalse
对调用地址的监控
内核的导出函数都是一些调用非常频繁的函数,每时每刻都会有驱动程序对他们进行调用。全部记录下来是非常不现实的事情,会导致系统完全卡死。因此这里需要通过返回地址对调用来源进行选择性判断,只打印来自特定来源的函数调用。本监控框架封装了一个用于维护监控地址集合的singleton。可以通过以下三个宏
123#define ADD_MONITOR_RANGE(start, end) smallzhong::MonitorAddressManager::GetInstance().AddMonitorRange((start), (end))#define DEL_FROM_MONITOR_LIST(addr) smallzhong::MonitorAddressManager::GetInstance().DelFromMonitorList((addr))#define FILTER_RET_ADDR(ret_addr) smallzhong::MonitorAddressManager::GetInstance().FilterRetAddr((ret_addr))来添加、删除监控范围,以及判断某一个地址是否正在被监控。
如下是IDA脚本自动生成的一个handler。可以看到使用了
FILTER_RET_ADDR判断调用来源,只有返回地址是特定来源的调用,才进行打印四个参数和返回地址的记录。12345678910BOOLEANhandler_c4a77d9f(PGuestContext context){ULONG64origin_ret_addr = *(PULONG64)(context->mRsp);if(FILTER_RET_ADDR(origin_ret_addr)){LOG_INFO("Function: ExAllocatePoolWithTag\nRCX: %llx, RDX: %llx, R8: %llx, R9: %llx\nReturn Address: %llx\n\n",context->mRcx, context->mRdx, context->mR8, context->mR9, origin_ret_addr);}returnFALSE;}
使用流程
使用nuget导入米松哥封装的 Musa.Runtime ,开始愉快地在内核编写C++代码
把需要监控的驱动用IDA打开,打开
scripts\AutoGen.py,ctrl + h 全局修改修改里面硬编码的保存路径后运行AutoGen.py脚本,得到available_funcs.inc、handlers.h、handlers.c三个自动生成的文件,并将其导入vs项目中。在 DriverMain 中特定 Hook 自己感兴趣的函数。
加载驱动,查看日志。
使用本框架对驱动进行分析,以2025腾讯游戏安全决赛题目为例
设置分析环境
在
DriverMain中设置 ImageCallback12345678EXTERN_C NTSTATUS DriverMain(const PDRIVER_OBJECT DriverObject, const PUNICODE_STRING Registry){LOG_INFO("entry\r\n");NTSTATUS status=STATUS_SUCCESS;status=PsSetLoadImageNotifyRoutine(ImageLoadCallback);...}在 callback 中检查是否为 ACEDriver.sys 被加载,如果是的话,添加相应监控范围。
1234567891011121314151617181920VOIDImageLoadCallback(PUNICODE_STRING FullImageName,HANDLEProcessId,PIMAGE_INFO ImageInfo){if(ProcessId == 0 && FullImageName != NULL){// 检查是否是 ACEDriver.sys 被加载if(wcsstr(FullImageName->Buffer, L"\\ACEDriver.sys")){LOG_INFO("ACEDriver.sys"" has been loaded!\n");LOG_INFO("Image Base: %p\n", ImageInfo->ImageBase);LOG_INFO("Image Size: %llx\n", ImageInfo->ImageSize);ADD_MONITOR_RANGE((ULONG64)ImageInfo->ImageBase, (ULONG64)ImageInfo->ImageBase + ImageInfo->ImageSize);}}}开启虚拟机,加载本分析框架。
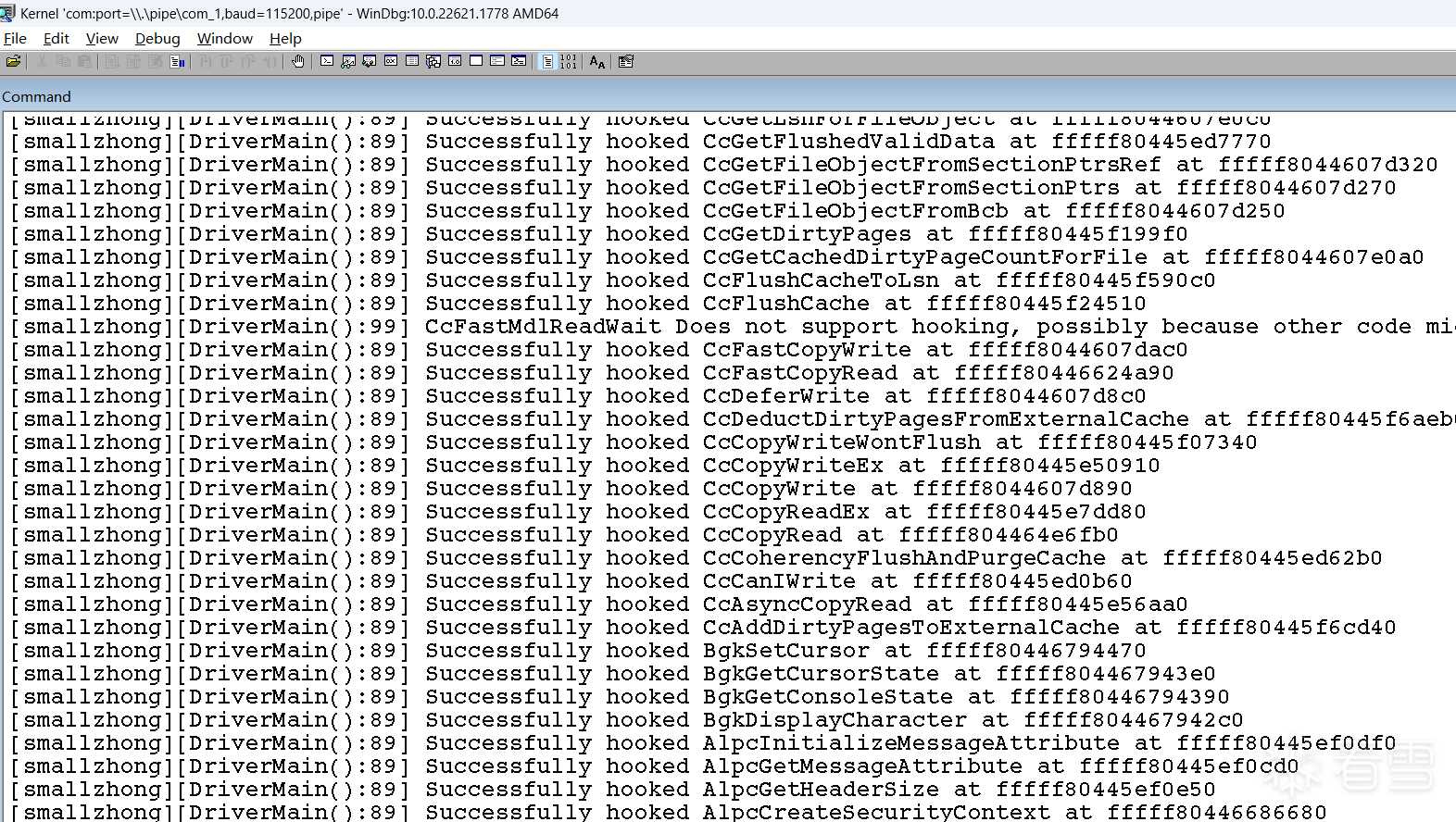
成功自动 hook 所有导出函数中可以hook的函数。
加载 ACEDriver.sys
- 加载后完整 log 如下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 | [smallzhong][ImageLoadCallback():22] ACEDriver.sys has been loaded![smallzhong][ImageLoadCallback():23] Image Base: FFFFF8044C9C0000[smallzhong][ImageLoadCallback():24] Image Size: 12ce000Function: ExAllocatePoolRCX: 200, RDX: 1a0, R8: fffff80445f331f0, R9: ffffbc84b35e7768Return Address: fffff8044d9eac91Function: NtQuerySystemInformationRCX: b, RDX: ffffbc84b35e7650, R8: 0, R9: ffffbc84b35e7648Return Address: fffff8044d7b062aFunction: ExAllocatePoolRCX: 200, RDX: 19960, R8: ffffbc84b35e7380, R9: ffffbc84b35e73e0Return Address: fffff8044d796230Function: NtQuerySystemInformationRCX: b, RDX: ffffd384236e6000, R8: 19960, R9: ffffbc84b35e7648Return Address: fffff8044d1259a8Function: ExFreePoolWithTagRCX: ffffd384236e6000, RDX: 0, R8: fffff80445e00000, R9: fffff80445e313e0Return Address: fffff8044d7ace2aFunction: IoAllocateMdlRCX: fffff8044c9c0000, RDX: 762537, R8: 0, R9: 0Return Address: fffff8044da92507Function: MmProbeAndLockPagesRCX: ffffd384269f0000, RDX: 0, R8: 1, R9: ffffbc84b35e7760Return Address: fffff8044dae65efFunction: MmMapLockedPagesSpecifyCacheRCX: ffffd384269f0000, RDX: 0, R8: 1, R9: 0Return Address: fffff8044db35827Function: ExAllocatePoolRCX: 200, RDX: 3e6c, R8: ffffbc84b35e7768, R9: fffffff86df59f7aReturn Address: fffff8044d97b359Function: ExFreePoolWithTagRCX: ffffd3842325f000, RDX: 0, R8: ffffbc84b35e7768, R9: 2Return Address: fffff8044d7dd486Function: NtQuerySystemInformationRCX: b, RDX: ffffbc84b35e7650, R8: 0, R9: ffffbc84b35e7648Return Address: fffff8044d7b062aFunction: ExAllocatePoolRCX: 200, RDX: 19960, R8: ffffbc84b35e7380, R9: ffffbc84b35e73e0Return Address: fffff8044d796230Function: NtQuerySystemInformationRCX: b, RDX: ffffd384236e6000, R8: 19960, R9: ffffbc84b35e7648Return Address: fffff8044d1259a8Function: ExFreePoolWithTagRCX: ffffd384236e6000, RDX: 0, R8: fffff80445e00000, R9: fffff80445e313e0Return Address: fffff8044d7ace2aFunction: NtQuerySystemInformationRCX: b, RDX: ffffbc84b35e7650, R8: 0, R9: ffffbc84b35e7648Return Address: fffff8044d7b062aFunction: ExAllocatePoolRCX: 200, RDX: 19960, R8: ffffbc84b35e7380, R9: ffffbc84b35e73e0Return Address: fffff8044d796230Function: NtQuerySystemInformationRCX: b, RDX: ffffd384236e6000, R8: 19960, R9: ffffbc84b35e7648Return Address: fffff8044d1259a8Function: ExFreePoolWithTagRCX: ffffd384236e6000, RDX: 0, R8: ffffbc84b35e766b, R9: ffffd384236e74d8Return Address: fffff8044d7ace2aFunction: KeSetSystemAffinityThreadRCX: 1, RDX: 8, R8: 0, R9: ffffbc84b35e7770Return Address: fffff8044d8c2bc1Function: KeSetSystemAffinityThreadRCX: 2, RDX: 8, R8: 0, R9: ffffbc84b35e7770Return Address: fffff8044d8c2bc1Function: KeSetSystemAffinityThreadRCX: 4, RDX: 8, R8: 0, R9: ffffbc84b35e7770Return Address: fffff8044d8c2bc1Function: KeSetSystemAffinityThreadRCX: 8, RDX: 8, R8: 0, R9: ffffbc84b35e7770Return Address: fffff8044d8c2bc1Function: KeRevertToUserAffinityThreadRCX: 0, RDX: 0, R8: ffffbc84b35e7778, R9: ffffffffe12f6b55Return Address: fffff8044d981c67Function: MmUnlockPagesRCX: ffffd384269f0000, RDX: 8, R8: 0, R9: ffffbc84b35e7660Return Address: fffff8044d9a16eaFunction: IoFreeMdlRCX: ffffd384269f0000, RDX: 8, R8: 542b35c7, R9: ffffbc84b35e7660Return Address: fffff8044d9d0743Function: RtlCopyUnicodeStringRCX: fffff8044ca2b518, RDX: ffffd38427abf000, R8: ffffbc84b35e6f60, R9: 10Return Address: fffff8044c9cde8cFunction: ExIsProcessorFeaturePresentRCX: a, RDX: ffffd38427abf000, R8: ffffbe8a8e013084, R9: fffff8044c9d3210Return Address: fffff8044c9ce70bFunction: RtlGetVersionRCX: ffffbc84b35e76f0, RDX: 7, R8: 2, R9: 1Return Address: fffff8044c9ce4d7Function: MmGetSystemRoutineAddressRCX: ffffbc84b35e76d8, RDX: 7, R8: 2, R9: 1Return Address: fffff8044c9ce4f7Function: NtQuerySystemInformationRCX: e3, RDX: ffffbc84b35e76d0, R8: 1, R9: 0Return Address: fffff8044c9ce516Function: ZwOpenSectionRCX: ffffbc84b35e7800, RDX: 5, R8: ffffbc84b35e7770, R9: 0Return Address: fffff8044c9cdbf0Function: ZwQuerySectionRCX: ffffffff80002114, RDX: 1, R8: ffffbc84b35e77a0, R9: 40Return Address: fffff8044c9cdc27Function: ObReferenceObjectByHandleRCX: ffffffff80002114, RDX: 5, R8: ffffd3841d2cfbc0, R9: 0Return Address: fffff8044c9cdc57Function: MmMapViewInSystemSpaceRCX: ffffbe8a81ea2350, RDX: ffffbc84b35e7768, R8: ffffbc84b35e7760, R9: fffff80445e00000Return Address: fffff8044c9cdc6fFunction: MmUnmapViewInSystemSpaceRCX: fffff80442c00000, RDX: be8a80ec7f880400, R8: ffffbc84b35e74e0, R9: ffffbc84b35e7748Return Address: fffff8044c9cdc92Function: ObfDereferenceObjectRCX: ffffbe8a81ea2350, RDX: 4b, R8: ffffd38420124134, R9: 4Return Address: fffff8044c9cdca1Function: ZwCloseRCX: ffffffff80002114, RDX: 4b, R8: ffffd38420124134, R9: 4Return Address: fffff8044c9cdcb0Function: ExInitializeResourceLiteRCX: fffff8044ca2b6e0, RDX: fffff8044ca2b6e0, R8: ffffffff, R9: 7fffbe8a81ea2330Return Address: fffff8044c9cebaeFunction: ExInitializeNPagedLookasideListRCX: fffff8044ca2b100, RDX: 0, R8: 0, R9: 200Return Address: fffff8044c9cb60cFunction: RtlInitializeGenericTableAvlRCX: fffff8044ca2b180, RDX: fffff8044c9cb460, R8: fffff8044c9cb450, R9: fffff8044c9cb480Return Address: fffff8044c9cb640Function: PsGetCurrentThreadIdRCX: ffffbc84b35e77e0, RDX: 0, R8: 0, R9: 0Return Address: fffff8044c9cb658Function: RtlInsertElementGenericTableAvlRCX: fffff8044ca2b180, RDX: ffffbc84b35e7760, R8: 90, R9: ffffbc84b35e7728Return Address: fffff8044c9cb4baFunction: ExAllocatePoolWithTagRCX: 200, RDX: b0, R8: 74726375, R9: ffffbc84b35e7728Return Address: fffff8044c9cb3aeFunction: ExInitializeResourceLiteRCX: fffff8044ca2b5a0, RDX: fffff8044ca2b5a0, R8: 0, R9: 0Return Address: fffff8044c9ceafeFunction: ExInitializeResourceLiteRCX: fffff8044ca2b608, RDX: fffff8044ca2b5a0, R8: 8, R9: 0Return Address: fffff8044c9ceafeFunction: ExInitializeResourceLiteRCX: fffff8044ca2b670, RDX: fffff8044ca2b5a0, R8: 0, R9: 0Return Address: fffff8044c9ceafeFunction: ExInitializeNPagedLookasideListRCX: fffff8044ca2b200, RDX: 0, R8: 0, R9: 200Return Address: fffff8044c9cda88Function: RtlInitializeGenericTableAvlRCX: fffff8044ca2b280, RDX: fffff8044c9cd8c0, R8: fffff8044c9cd8b0, R9: fffff8044c9cd8e0Return Address: fffff8044c9cdabcFunction: PsGetCurrentThreadIdRCX: ffffbc84b35e77e8, RDX: 0, R8: 0, R9: 0Return Address: fffff8044c9cdad2Function: RtlInsertElementGenericTableAvlRCX: fffff8044ca2b280, RDX: ffffbc84b35e77a0, R8: 48, R9: ffffbc84b35e7768Return Address: fffff8044c9cd946Function: ExAllocatePoolWithTagRCX: 200, RDX: 68, R8: 74726375, R9: ffffbc84b35e7768Return Address: fffff8044c9cb3aeFunction: ExAllocatePoolWithTagRCX: 200, RDX: 1c0, R8: 74726375, R9: 0Return Address: fffff8044c9cd45fFunction: RtlGetVersionRCX: ffffd3842409a84c, RDX: 11c, R8: 0, R9: fffReturn Address: fffff8044c9c8cc7Function: ZwQuerySystemInformationRCX: b, RDX: 0, R8: 0, R9: ffffbc84b35e77d8Return Address: fffff8044d122066Function: ExAllocatePoolWithTagRCX: 0, RDX: ccb0, R8: 6d6f646c, R9: ffffbc84b35e73c0Return Address: fffff8044d12206cFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38429406000, R8: ccb0, R9: ffffbc84b35e77d8Return Address: fffff8044d122074Function: ExFreePoolWithTagRCX: ffffd38429406000, RDX: 6d6f646c, R8: ffffbc84b35e7300, R9: ffffbc84b35e73c0Return Address: fffff8044d122091Function: ZwQuerySystemInformationRCX: b, RDX: 0, R8: 0, R9: ffffbc84b35e77d8Return Address: fffff8044d1220b9Function: ExAllocatePoolWithTagRCX: 0, RDX: ccb0, R8: 6d6f646c, R9: ffffbc84b35e73c0Return Address: fffff8044d1220bfFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38429406000, R8: ccb0, R9: ffffbc84b35e77d8Return Address: fffff8044d1220c5Function: ExFreePoolWithTagRCX: ffffd38429406000, RDX: 6d6f646c, R8: ffffbc84b35e7300, R9: ffffbc84b35e73c0Return Address: fffff8044d1220d2Function: ExAllocatePoolWithTagRCX: 1, RDX: 1000, R8: 35384245, R9: 0Return Address: fffff8044d122252Function: ExAllocatePoolWithTagRCX: 200, RDX: 20, R8: 44533143, R9: 0Return Address: fffff8044d121f98Function: ExQueueWorkItemRCX: ffffd384233ee550, RDX: 1, R8: ffffd384233ee550, R9: fffReturn Address: fffff8044d121fefFunction: KeDelayExecutionThreadRCX: 0, RDX: 0, R8: ffffbc84b28cab38, R9: 0Return Address: fffff8044d1209b1Function: KeDelayExecutionThreadRCX: 0, RDX: 0, R8: ffffbc84b35e7808, R9: 2fReturn Address: fffff8044d1209b1Function: ZwQuerySystemInformationRCX: b, RDX: 0, R8: 0, R9: ffffbc84b28cab38Return Address: fffff8044d1209e2Function: ExAllocatePoolWithTagRCX: 0, RDX: ccb0, R8: 6d6f646c, R9: ffffbc84b28ca720Return Address: fffff8044d1209f4Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38429406000, R8: ccb0, R9: ffffbc84b28cab38Return Address: fffff8044d1209faFunction: ExFreePoolWithTagRCX: ffffd38429406000, RDX: 6d6f646c, R8: ffffbc84b28ca600, R9: ffffbc84b28ca720Return Address: fffff8044d120a3fFunction: KdRefreshDebuggerNotPresentRCX: fffff80446796028, RDX: 3bd, R8: fffff80446796000, R9: 188b5e66ecc8b28Return Address: fffff8044d121634KDTARGET: Refreshing KD connectionFunction: ZwQuerySystemInformationRCX: b, RDX: 0, R8: 0, R9: ffffbc84b28caaa8Return Address: fffff8044d120bc2Function: ExAllocatePoolWithTagRCX: 0, RDX: ccb0, R8: 6d6f646c, R9: ffffbc84b28ca690Return Address: fffff8044d120bdcFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38429406000, R8: ccb0, R9: ffffbc84b28caaa8Return Address: fffff8044d120be2Function: ExFreePoolWithTagRCX: ffffd38429406000, RDX: 6d6f646c, R8: ffffbc84b28ca600, R9: ffffbc84b28ca690Return Address: fffff8044d120bfbFunction: ExAllocatePoolWithTagRCX: 0, RDX: 40, R8: 41434520, R9: 882b074c4af83a16Return Address: fffff8044d121195Function: KeInitializeDpcRCX: ffffd3841cd025d0, RDX: fffff8044c9c78c0, R8: fffff80445fc14e0, R9: fffReturn Address: fffff8044d1211d7Function: KeInsertQueueDpcRCX: ffffd3841cd025d0, RDX: 0, R8: 0, R9: fffReturn Address: fffff8044d121205KDTARGET: Refreshing KD connection*** Fatal System Error: 0x00414345 (0x0000000000000000,0x0000000000000000,0x0000000000000000,0x0000000000000000)Break instruction exception - code 80000003 (first chance)A fatal system error has occurred.Debugger entered on first try; Bugcheck callbacks have not been invoked.A fatal system error has occurred.For analysis of this file, run !analyze -vnt!DbgBreakPointWithStatus:fffff804`45fc9370 cc int 3 |
可以看到,中间出现了一次 KDTARGET: Refreshing KD connection 信息,再往上看,发现是 KdRefreshDebuggerNotPresent 函数被调用了。也就是说其使用了这个函数进行反调试。返回地址是 fffff8044d121634 ,imagebase是 FFFFF8044C9C0000 ,算出对这个函数进行调用的位置是 ACEDriver.sys + 0X761634 。直接通过dump的代码进入这个位置,发现这里是一个 ExQueueWorkItem 起来的线程,从log中也可以看出来调用了 ExQueueWorkItem 。最终分析得出结论:需要 hook KdDisableDebugger 和 KdRefreshDebuggerNotPresent 两个函数,并手动设置返回值。实现如下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 | if (func.function_name == "KdDisableDebugger"){ auto lambda = [](GuestContext* context) -> BOOLEAN { ULONG64 origin_ret_addr = *(PULONG64)(context->mRsp); if (FILTER_RET_ADDR(origin_ret_addr)) { LOG_INFO("Function: KdDisableDebugger\nRCX: %llx, RDX: %llx, R8: %llx, R9: %llx\nReturn Address: %llx\n\n", context->mRcx, context->mRdx, context->mR8, context->mR9, origin_ret_addr); } context->mRax = STATUS_SUCCESS; return TRUE; }; try { GLOBAL_HOOK_MANAGER.add_hook(func.address, reinterpret_cast<ULONG64>(+lambda)); LOG_INFO("Successfully hooked %s at %llx\r\n", func.function_name.c_str(), func.address); } catch (const std::exception& e) { LOG_INFO("Failed to hook %s: %s\r\n", func.function_name.c_str(), e.what()); }}else if (func.function_name == "KdRefreshDebuggerNotPresent"){ //DbgBreakPoint(); auto lambda = [](GuestContext* context) -> BOOLEAN { ULONG64 origin_ret_addr = *(PULONG64)(context->mRsp); if (FILTER_RET_ADDR(origin_ret_addr)) { LOG_INFO("Function: KdRefreshDebuggerNotPresent\nRCX: %llx, RDX: %llx, R8: %llx, R9: %llx\nReturn Address: %llx\n\n", context->mRcx, context->mRdx, context->mR8, context->mR9, origin_ret_addr); } context->mRax = 1; return TRUE; }; try { GLOBAL_HOOK_MANAGER.add_hook(func.address, reinterpret_cast<ULONG64>(+lambda)); LOG_INFO("Successfully hooked %s at %llx\r\n", func.function_name.c_str(), func.address); } catch (const std::exception& e) { LOG_INFO("Failed to hook %s: %s\r\n", func.function_name.c_str(), e.what()); }} |
在 handler 里面直接修改 mRax 返回值,并 return TRUE 。在本框架中, return TRUE 是不调用原始函数,设置寄存器后直接返回。因此效果是,调用 KdDisableDebugger 直接返回 STATUS_SUCCESS ,不调用原始函数。调用 KdRefreshDebuggerNotPresent 返回1,这个值表明当前没有挂上调试器。在加上这两个函数的hook后,重新加载驱动。
hook后再次加载 ACEDriver.sys
把前文说到的相关hook加上后再次加载,这次不会蓝屏了。完整log如下
123456789101112131415161718192021222324252627282930313233343536373839404142434445464748495051525354555657585960616263646566676869707172737475767778798081828384858687888990919293949596979899100101102103104105106107108109110111112113114115116117118119120121122123124125126127128129130131132133134135136137138139140141142143144145146147148149150151152153154155156157158159160161162163164165166167168169170171172173174175176177178179180181182183184185186187188189190191192193194195196197198199200201202203204205206207208209210211212213214215216217218219220221222223224225226227228229230231232233234235236237238239240241242243244245246247248249250251252253254255256257258259260261262263264265266267268269270271272273274275276277278279280281282283284285286287288289290291292293294295296297298299300301302303304305306307308309310311312313314315316317318319320321322323324325326327328329330331332333334335336337338339340341342343344345346347348349350351352353354355356357358359360361362363364365366367368369370371372373374375376377378379380381382383384385386387388389390391392393394395396397398399400401402403404405406407408409410411412413414415416417418419420421422423424425426427428429430431432433434435436437438439440441442443444445446447448449450451452453454455456457458459460461462463464465466467468469470471472473474475476477478479480481482483484485486487488489490491492493494495496497498499500501502503504505506507508509510511512513514515516517518519520521522523524525526527528529530531532533534535536537538539540541542543544545546547548549550551552553554555556557558559560561562563564565566567568569570571572573574575576577578579580581582583584585586587588589590591592593594595596597598599600601602603604605606607608609610611612613614615616617618619620621622623624625626627628629630631632633634635636637638639640641642643644645646647648649650651652653654655656657658659660661662663664665666667668669670671672673674675676677678679680681682683684685686687688689690691692693694695696697698699700701702703704705706707708709710711712713714715716717718719720721722723724725726727728729730731732733734735736737738739740741742743744745746747748749750751752753754755756757758759760761762763764765766767768769770771[smallzhong][ImageLoadCallback():22] ACEDriver.sys has been loaded![smallzhong][ImageLoadCallback():23] Image Base: FFFFF8044CFA0000[smallzhong][ImageLoadCallback():24] Image Size:12ce000Function: ExAllocatePoolRCX:200, RDX:1a0, R8: fffff80445f331f0, R9: ffffbc84b35d2768Return Address: fffff8044dfcac91Function: NtQuerySystemInformationRCX: b, RDX: ffffbc84b35d2650, R8:0, R9: ffffbc84b35d2648Return Address: fffff8044dd9062aFunction: ExAllocatePoolRCX:200, RDX:19710, R8: ffffbc84b35d2380, R9: ffffbc84b35d23e0Return Address: fffff8044dd76230Function: NtQuerySystemInformationRCX: b, RDX: ffffd384234c5000, R8:19710, R9: ffffbc84b35d2648Return Address: fffff8044d7059a8Function: ExFreePoolWithTagRCX: ffffd384234c5000, RDX:0, R8: fffff80445e00000, R9: fffff80445e313e0Return Address: fffff8044dd8ce2aFunction: IoAllocateMdlRCX: fffff8044cfa0000, RDX:762537, R8:0, R9:0Return Address: fffff8044e072507Function: MmProbeAndLockPagesRCX: ffffd384233e2000, RDX:0, R8:1, R9: ffffbc84b35d2760Return Address: fffff8044e0c65efFunction: MmMapLockedPagesSpecifyCacheRCX: ffffd384233e2000, RDX:0, R8:1, R9:0Return Address: fffff8044e115827Function: ExAllocatePoolRCX:200, RDX:3e6c, R8: ffffbc84b35d2768, R9: fffffff86df59f7aReturn Address: fffff8044df5b359Function: ExFreePoolWithTagRCX: ffffd38422dc8000, RDX:0, R8: ffffbc84b35d2768, R9:2Return Address: fffff8044ddbd486Function: NtQuerySystemInformationRCX: b, RDX: ffffbc84b35d2650, R8:0, R9: ffffbc84b35d2648Return Address: fffff8044dd9062aFunction: ExAllocatePoolRCX:200, RDX:19710, R8: ffffbc84b35d2380, R9: ffffbc84b35d23e0Return Address: fffff8044dd76230Function: NtQuerySystemInformationRCX: b, RDX: ffffd384234c5000, R8:19710, R9: ffffbc84b35d2648Return Address: fffff8044d7059a8Function: ExFreePoolWithTagRCX: ffffd384234c5000, RDX:0, R8: fffff80445e00000, R9: fffff80445e313e0Return Address: fffff8044dd8ce2aFunction: NtQuerySystemInformationRCX: b, RDX: ffffbc84b35d2650, R8:0, R9: ffffbc84b35d2648Return Address: fffff8044dd9062aFunction: ExAllocatePoolRCX:200, RDX:19710, R8: ffffbc84b35d2380, R9: ffffbc84b35d23e0Return Address: fffff8044dd76230Function: NtQuerySystemInformationRCX: b, RDX: ffffd384234c5000, R8:19710, R9: ffffbc84b35d2648Return Address: fffff8044d7059a8Function: ExFreePoolWithTagRCX: ffffd384234c5000, RDX:0, R8: ffffbc84b35d266b, R9: ffffd384234c64d8Return Address: fffff8044dd8ce2aFunction: KeSetSystemAffinityThreadRCX:1, RDX:8, R8:0, R9: ffffbc84b35d2770Return Address: fffff8044dea2bc1Function: KeSetSystemAffinityThreadRCX:2, RDX:8, R8:0, R9: ffffbc84b35d2770Return Address: fffff8044dea2bc1Function: KeSetSystemAffinityThreadRCX:4, RDX:8, R8:0, R9: ffffbc84b35d2770Return Address: fffff8044dea2bc1Function: KeSetSystemAffinityThreadRCX:8, RDX:8, R8:0, R9: ffffbc84b35d2770Return Address: fffff8044dea2bc1Function: KeRevertToUserAffinityThreadRCX:0, RDX:0, R8: ffffbc84b35d2778, R9: ffffffffe12f6b55Return Address: fffff8044df61c67Function: MmUnlockPagesRCX: ffffd384233e2000, RDX:8, R8:0, R9: ffffbc84b35d2660Return Address: fffff8044df816eaFunction: IoFreeMdlRCX: ffffd384233e2000, RDX:8, R8:542b35c7, R9: ffffbc84b35d2660Return Address: fffff8044dfb0743Function: RtlCopyUnicodeStringRCX: fffff8044d00b518, RDX: ffffd38423134000, R8: ffffbc84b35d1f60, R9:10Return Address: fffff8044cfade8cFunction: ExIsProcessorFeaturePresentRCX: a, RDX: ffffd38423134000, R8: ffffffffffff3fff, R9: fffff8044cfb3210Return Address: fffff8044cfae70bFunction: RtlGetVersionRCX: ffffbc84b35d26f0, RDX:7, R8:2, R9:1Return Address: fffff8044cfae4d7Function: MmGetSystemRoutineAddressRCX: ffffbc84b35d26d8, RDX:7, R8:2, R9:1Return Address: fffff8044cfae4f7Function: NtQuerySystemInformationRCX: e3, RDX: ffffbc84b35d26d0, R8:1, R9:0Return Address: fffff8044cfae516Function: ZwOpenSectionRCX: ffffbc84b35d2800, RDX:5, R8: ffffbc84b35d2770, R9:0Return Address: fffff8044cfadbf0Function: ZwQuerySectionRCX: ffffffff80002b70, RDX:1, R8: ffffbc84b35d27a0, R9:40Return Address: fffff8044cfadc27Function: ObReferenceObjectByHandleRCX: ffffffff80002b70, RDX:5, R8: ffffd3841d2cfbc0, R9:0Return Address: fffff8044cfadc57Function: MmMapViewInSystemSpaceRCX: ffffbe8a81ea2350, RDX: ffffbc84b35d2768, R8: ffffbc84b35d2760, R9: fffff80445e00000Return Address: fffff8044cfadc6fFunction: MmUnmapViewInSystemSpaceRCX: fffff80442c00000, RDX: be8a80ec7f880400, R8: ffffbc84b35d24e0, R9: ffffbc84b35d2748Return Address: fffff8044cfadc92Function: ObfDereferenceObjectRCX: ffffbe8a81ea2350, RDX: ac, R8: ffffd3842323415a, R9:2aReturn Address: fffff8044cfadca1Function: ZwCloseRCX: ffffffff80002b70, RDX: ac, R8: ffffd3842323415a, R9:2aReturn Address: fffff8044cfadcb0Function: ExInitializeResourceLiteRCX: fffff8044d00b6e0, RDX: fffff8044d00b6e0, R8: ffffffff, R9:7fffbe8a81ea2330Return Address: fffff8044cfaebaeFunction: ExInitializeNPagedLookasideListRCX: fffff8044d00b100, RDX:0, R8:0, R9:200Return Address: fffff8044cfab60cFunction: RtlInitializeGenericTableAvlRCX: fffff8044d00b180, RDX: fffff8044cfab460, R8: fffff8044cfab450, R9: fffff8044cfab480Return Address: fffff8044cfab640Function: PsGetCurrentThreadIdRCX: ffffbc84b35d27e0, RDX:0, R8:0, R9:0Return Address: fffff8044cfab658Function: RtlInsertElementGenericTableAvlRCX: fffff8044d00b180, RDX: ffffbc84b35d2760, R8:90, R9: ffffbc84b35d2728Return Address: fffff8044cfab4baFunction: ExAllocatePoolWithTagRCX:200, RDX: b0, R8:74726375, R9: ffffbc84b35d2728Return Address: fffff8044cfab3aeFunction: ExInitializeResourceLiteRCX: fffff8044d00b5a0, RDX: fffff8044d00b5a0, R8:0, R9:0Return Address: fffff8044cfaeafeFunction: ExInitializeResourceLiteRCX: fffff8044d00b608, RDX: fffff8044d00b5a0, R8:8, R9:0Return Address: fffff8044cfaeafeFunction: ExInitializeResourceLiteRCX: fffff8044d00b670, RDX: fffff8044d00b5a0, R8:0, R9:0Return Address: fffff8044cfaeafeFunction: ExInitializeNPagedLookasideListRCX: fffff8044d00b200, RDX:0, R8:0, R9:200Return Address: fffff8044cfada88Function: RtlInitializeGenericTableAvlRCX: fffff8044d00b280, RDX: fffff8044cfad8c0, R8: fffff8044cfad8b0, R9: fffff8044cfad8e0Return Address: fffff8044cfadabcFunction: PsGetCurrentThreadIdRCX: ffffbc84b35d27e8, RDX:0, R8:0, R9:0Return Address: fffff8044cfadad2Function: RtlInsertElementGenericTableAvlRCX: fffff8044d00b280, RDX: ffffbc84b35d27a0, R8:48, R9: ffffbc84b35d2768Return Address: fffff8044cfad946Function: ExAllocatePoolWithTagRCX:200, RDX:68, R8:74726375, R9: ffffbc84b35d2768Return Address: fffff8044cfab3aeFunction: ExAllocatePoolWithTagRCX:200, RDX:1c0, R8:74726375, R9:0Return Address: fffff8044cfad45fFunction: RtlGetVersionRCX: ffffd3841de7b2bc, RDX:11c, R8:0, R9: fffReturn Address: fffff8044cfa8cc7Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35d27d8Return Address: fffff8044d702066Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35d23c0Return Address: fffff8044d70206cFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35d27d8Return Address: fffff8044d702074Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35d2300, R9: ffffbc84b35d23c0Return Address: fffff8044d702091Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35d27d8Return Address: fffff8044d7020b9Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35d23c0Return Address: fffff8044d7020bfFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35d27d8Return Address: fffff8044d7020c5Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35d2300, R9: ffffbc84b35d23c0Return Address: fffff8044d7020d2Function: ExAllocatePoolWithTagRCX:1, RDX:1000, R8:35384245, R9:0Return Address: fffff8044d702252Function: ExAllocatePoolWithTagRCX:200, RDX:20, R8:44533143, R9:0Return Address: fffff8044d701f98Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffReturn Address: fffff8044d701fefFunction: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35d2808, R9:2fReturn Address: fffff8044d7009b1Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b27f0b38, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b27f0b38Return Address: fffff8044d7009e2Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b27f0720Return Address: fffff8044d7009f4Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b27f0b38Return Address: fffff8044d7009faFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b27f0600, R9: ffffbc84b27f0720Return Address: fffff8044d700a3f[smallzhong][DriverMain::<lambda_2>::operator ()():111] Function: KdRefreshDebuggerNotPresentRCX: fffff80446796028, RDX:3bd, R8: fffff80446796000, R9:188b5e66ecc8b28Return Address: fffff8044d701634Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:188b5e66ecc8b28Return Address: fffff8044d7016c0Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b28c3af8, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b28c3af8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b28c36e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b28c3af8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b28c3600, R9: ffffbc84b28c36e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b28c3af8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b28c36e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b28c3af8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b28c3600, R9: ffffbc84b28c36e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b28c3b80, R8: ffffbc84b28c3b78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b27f0b38, R9:0Return Address: fffff8044d7009b1Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffff80445e00000Return Address: fffff8044d701e86Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35fcaf8, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b35fcb80, R8: ffffbc84b35fcb78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b350eb38, R9:0Return Address: fffff8044d7009b1Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffff80445e00000Return Address: fffff8044d701e86Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35fcaf8, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b35fcb80, R8: ffffbc84b35fcb78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b350eb38, R9:0Return Address: fffff8044d7009b1Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffff80445e00000Return Address: fffff8044d701e86Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35fcaf8, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b35fcb80, R8: ffffbc84b35fcb78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b27f0b38, R9:0Return Address: fffff8044d7009b1Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffff80445e00000Return Address: fffff8044d701e86Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35fcaf8, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b35fcb80, R8: ffffbc84b35fcb78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b28c3b38, R9:0Return Address: fffff8044d7009b1Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffff80445e00000Return Address: fffff8044d701e86Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35fcaf8, R9:0Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b35fcaf8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b35fc600, R9: ffffbc84b35fc6e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b35fcb80, R8: ffffbc84b35fcb78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b28c3b38, R9:0Return Address: fffff8044d7009b1Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9: fffff80445e00000Return Address: fffff8044d701e86Function: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b27f0af8, R9:0Return Address: fffff8044d7009b1Function: KeQueryActiveProcessorCountRCX:0, RDX:0, R8:0, R9:0Return Address: fffff8044d6ff80fFunction: ExAllocatePoolWithTagRCX:200, RDX:9d4000, R8:41316333, R9:0Return Address: fffff8044d6ff85cFunction: KeDelayExecutionThreadRCX:0, RDX:0, R8: ffffbc84b35d2808, R9:689Return Address: fffff8044d7009b1Function: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b27f0af8Return Address: fffff8044d700a81Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b27f06e0Return Address: fffff8044d700a87Function: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b27f0af8Return Address: fffff8044d700a8dFunction: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b27f0600, R9: ffffbc84b27f06e0Return Address: fffff8044d700b02[smallzhong][DriverMain::<lambda_1>::operator ()():87] Function: KdDisableDebuggerRCX: fffff80446796028, RDX:3b4, R8: fffff80446796000, R9: abb86a985761b61Return Address: fffff8044d7018fdFunction: ZwQuerySystemInformationRCX: b, RDX:0, R8:0, R9: ffffbc84b27f0af8Return Address: fffff8044d700b37Function: ExAllocatePoolWithTagRCX:0, RDX: cb88, R8:6d6f646c, R9: ffffbc84b27f06e0Return Address: fffff8044d700b3dFunction: ZwQuerySystemInformationRCX: b, RDX: ffffd38425606000, R8: cb88, R9: ffffbc84b27f0af8Return Address: fffff8044d700b43Function: ExFreePoolWithTagRCX: ffffd38425606000, RDX:6d6f646c, R8: ffffbc84b27f0600, R9: ffffbc84b27f06e0Return Address: fffff8044d700b87Function: ZwProtectVirtualMemoryRCX: ffffffffffffffff, RDX: ffffbc84b27f0b80, R8: ffffbc84b27f0b78, R9:40Return Address: fffff8044d701b36Function: ExQueueWorkItemRCX: ffffd38420034940, RDX:1, R8: ffffd38420034940, R9:0Return Address: fffff8044d701c02Function: ExFreePoolWithTagRCX: ffffd38420034940, RDX:44533143, R8:20, R9:0Return Address: fffff8044d701e86Function: ExFreePoolWithTagRCX: ffffbe8a89381000, RDX:35384245, R8: ffffd3841d269040, R9: fffff80445e00000Return Address: fffff8044d701f3dFunction: ExFreePoolWithTagRCX: ffffd3841de7b290, RDX:74726375, R8: ffffbc84b35d26b8, R9: ffffffffReturn Address: fffff8044cfad885Function: ExEnterCriticalRegionAndAcquireResourceExclusiveRCX: fffff8044d00b5a0, RDX: ffffbc84b35d2840, R8: ffffbc84b35d2848, R9: ffffbc84b35d2878Return Address: fffff8044cfae5acFunction: ExEnterCriticalRegionAndAcquireResourceExclusiveRCX: fffff8044d00b5a0, RDX: ffffbc84b35d27c8, R8: ffffbc84b35d2790, R9: ffffbc84b35d27c0Return Address: fffff8044cfae895Function: ExReleaseResourceAndLeaveCriticalRegionRCX: fffff8044d00b5a0, RDX: fffff8044d00b568, R8:641e7b808835, R9: ffffbc84b35d27c0Return Address: fffff8044cfae9c2Function: ExReleaseResourceAndLeaveCriticalRegionRCX: fffff8044d00b5a0, RDX: fffff8044cfb0240, R8: ffffbc84b35d26d0, R9: ffffbc84b35d27c0Return Address: fffff8044cfae5bdFunction: RtlGetElementGenericTableAvlRCX: fffff8044d00b280, RDX:0, R8: ffffbc84b35d27c0, R9: ffffbc84b35d27c0Return Address: fffff8044cfadb45Function: RtlDeleteElementGenericTableAvlRCX: fffff8044d00b280, RDX: ffffd384232486b0, R8:0, R9:0Return Address: fffff8044cfadb36Function: RtlGetElementGenericTableAvlRCX: fffff8044d00b280, RDX:0, R8:0, R9:0Return Address: fffff8044cfadb45Function: ExDeleteNPagedLookasideListRCX: fffff8044d00b200, RDX:0, R8:0, R9:0Return Address: fffff8044cfadb57Function: ExDeleteResourceLiteRCX: fffff8044d00b670, RDX:8f, R8: ffffd3842323415a, R9:2aReturn Address: fffff8044cfaeb66Function: ExDeleteResourceLiteRCX: fffff8044d00b608, RDX:0, R8: ffffd3842323415a, R9:2aReturn Address: fffff8044cfaeb66Function: ExDeleteResourceLiteRCX: fffff8044d00b5a0, RDX:0, R8: ffffd3842323415a, R9:2aReturn Address: fffff8044cfaeb66Function: RtlGetElementGenericTableAvlRCX: fffff8044d00b180, RDX:0, R8: ffffd3842323415a, R9:2aReturn Address: fffff8044cfab6c9Function: RtlDeleteElementGenericTableAvlRCX: fffff8044d00b180, RDX: ffffd38422954f40, R8:0, R9:0Return Address: fffff8044cfab6baFunction: RtlGetElementGenericTableAvlRCX: fffff8044d00b180, RDX:0, R8:0, R9:0Return Address: fffff8044cfab6c9Function: ExDeleteNPagedLookasideListRCX: fffff8044d00b100, RDX:0, R8:0, R9:0Return Address: fffff8044cfab6dbFunction: ExDeleteResourceLiteRCX: fffff8044d00b6e0, RDX:27, R8: ffffd384229431ac, R9:24Return Address: fffff8044cfaebf6Function: DbgPrintExRCX:4d, RDX:0, R8: fffff8044cfb0840, R9: c0000001Return Address: fffff8044cfadf0cDriverEntry failed0xc0000001fordriver \REGISTRY\MACHINE\SYSTEM\ControlSet001\Services\ACEDriverFunction: ExFreePoolWithTagRCX: ffffd38422ef9e00, RDX:0, R8:140d712a4, R9:2Return Address: fffff8044e053193可以看到,会两个workitem互相调用,后面应该是 HV 的 EPT 相关信息的申请和保存,也可以通过这些函数的调用地点反推到关键函数。接下来的分析就不写了。因为找到关键算法位置之后就是令人头晕的逆向环节。本框架只能用来快速定位整个驱动的关键逻辑点,但是逆向工作还是需要自己手动通过打印出来的返回地址回溯并手工逆向。
更多【软件逆向-驱动挂钩所有内核导出函数来进行驱动逻辑分析】相关视频教程:www.yxfzedu.com
相关文章推荐
- 二进制漏洞-初探内核漏洞:HEVD学习笔记——TypeConfusion - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-初探内核漏洞:HEVD学习笔记——IntegerOverflow - PwnHarmonyOSWeb安全软件逆向
- 软件逆向-LMCompatibilityLevel 安全隐患 - PwnHarmonyOSWeb安全软件逆向
- Android安全-记一次完整的Android native层动态调试--使用avd虚拟机 - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-零基础入门V8——CVE-2021-38001漏洞利用 - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-初探内核漏洞:HEVD学习笔记——UAF - PwnHarmonyOSWeb安全软件逆向
- Pwn-glibc高版本堆题攻击之safe unlink - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-CVE-2020-1054提权漏洞学习笔记 - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-初探内核漏洞:HEVD学习笔记——BufferOverflowNonPagedPool - PwnHarmonyOSWeb安全软件逆向
- CTF对抗-2022DASCTF Apr X FATE 防疫挑战赛-Reverse-奇怪的交易 - PwnHarmonyOSWeb安全软件逆向
- 编程技术-一个规避安装包在当前目录下被DLL劫持的想法 - PwnHarmonyOSWeb安全软件逆向
- CTF对抗-sql注入学习笔记 - PwnHarmonyOSWeb安全软件逆向
- Pwn-DamCTF and Midnight Sun CTF Qualifiers pwn部分wp - PwnHarmonyOSWeb安全软件逆向
- 软件逆向-OLLVM-deflat 脚本学习 - PwnHarmonyOSWeb安全软件逆向
- 软件逆向-3CX供应链攻击样本分析 - PwnHarmonyOSWeb安全软件逆向
- Android安全-某艺TV版 apk 破解去广告及源码分析 - PwnHarmonyOSWeb安全软件逆向
- Pwn-Hack-A-Sat 4 Qualifiers pwn部分wp - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞- AFL 源代码速通笔记 - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-Netatalk CVE-2018-1160 复现及漏洞利用思路 - PwnHarmonyOSWeb安全软件逆向
- 二进制漏洞-DynamoRIO源码分析(一)--劫持进程 - PwnHarmonyOSWeb安全软件逆向
2):严禁色情、血腥、暴力
3):严禁发布任何形式的广告贴
4):严禁发表关于中国的政治类话题
5):严格遵守中国互联网法律法规
6):有侵权,疑问可发邮件至service@yxfzedu.com